Access Management
Based on your use case, the following feature can help your organization to maximize shared account security.
Also, we will ensure to boost your members' productivity at the same time without blocking them from accessing the account they need.
Per User Account
Members have their own individual account, either control by themself or the company can entering credentials.
On-premise/Cloud
we cover all popular SaaS services, or ping us to help with your on-premise app.
Company Managed Credential
manager assign credential to users by using password generator for higher security purpose.
Audit Log
All operation in Junify are traceable with timestamps, action, and operator.
Access Policy
Based on your shared account usage to customize the access requirement for authorized users.
Session Recording
all actions, mouse movements, and clicks can be recorded records while authorized user using the shared account.
2FA Handling
Junify can present authorized users with a 2FA code that it received from those services.
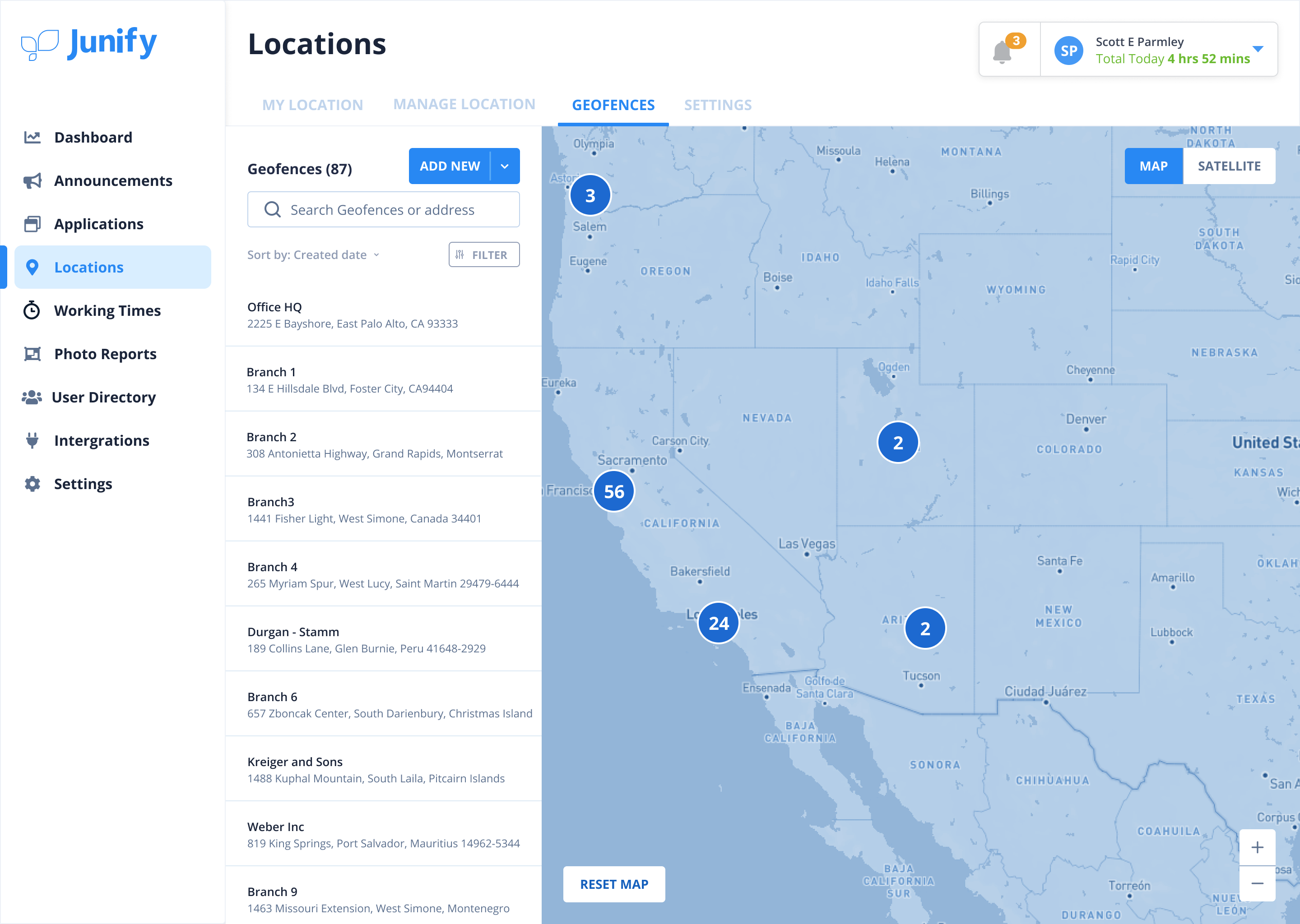
Location Control
To limit the account usage only within register geofence.
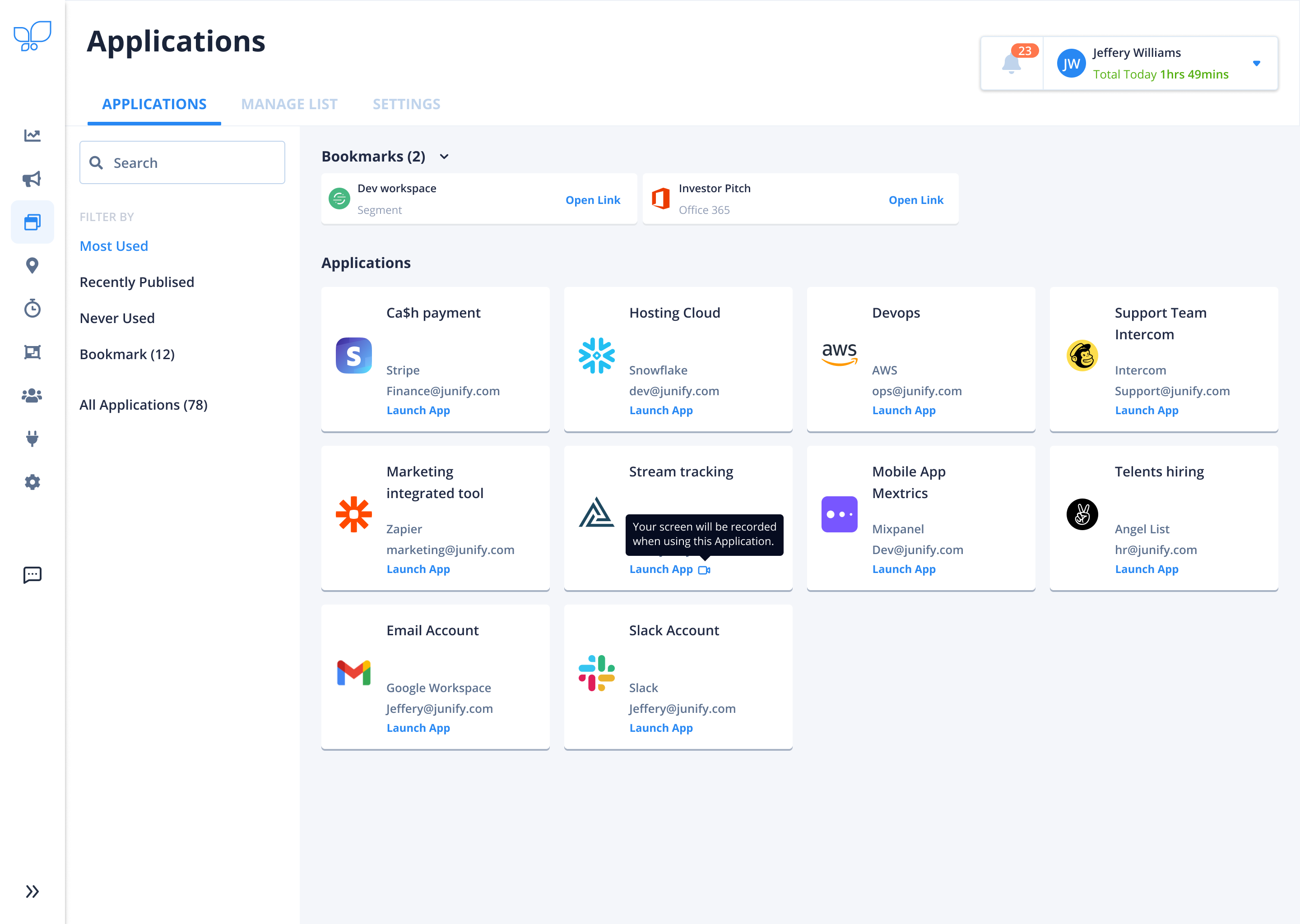
Coming soon!Application Launchpad
Members receive the account credential as an Application Card, or it can also be a Bookmark with a deep link to land on a specific page. All they need is to launch it with one click by our Zero Sign-On® technology!
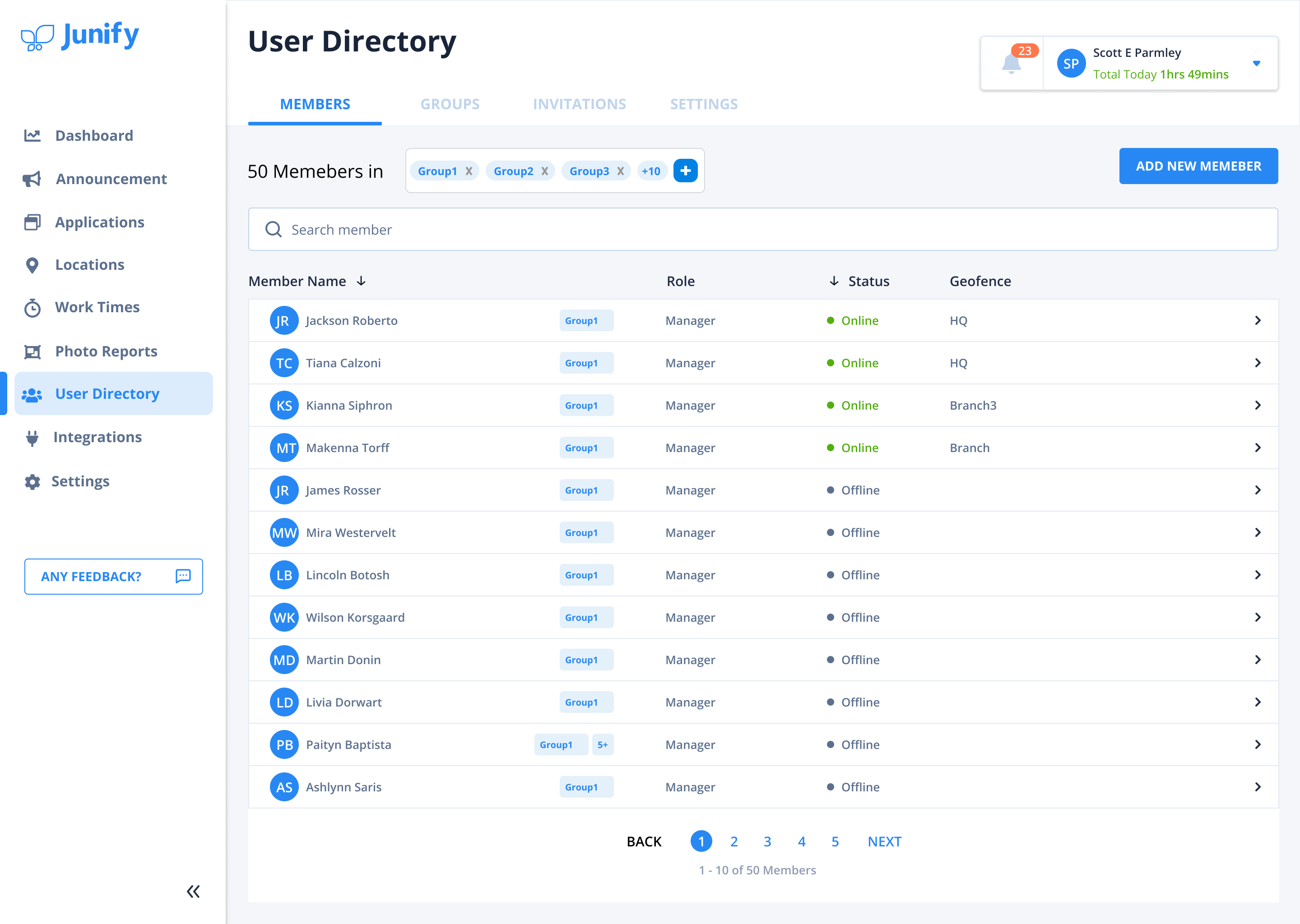
User Management
Hiring the right talents could take months but onboarding them to junify only needs seconds. Assign them to the belonging group, and they can use the authorized applications on their first day! When it’s time to say goodbye, lose all account access within clicks.
Inviting members in sec
Junify will send a 6-digit code by SMS or QR code by email to assist in onboard your members.
Integrate with Active Directory
Simply import your member list from Active Directory.
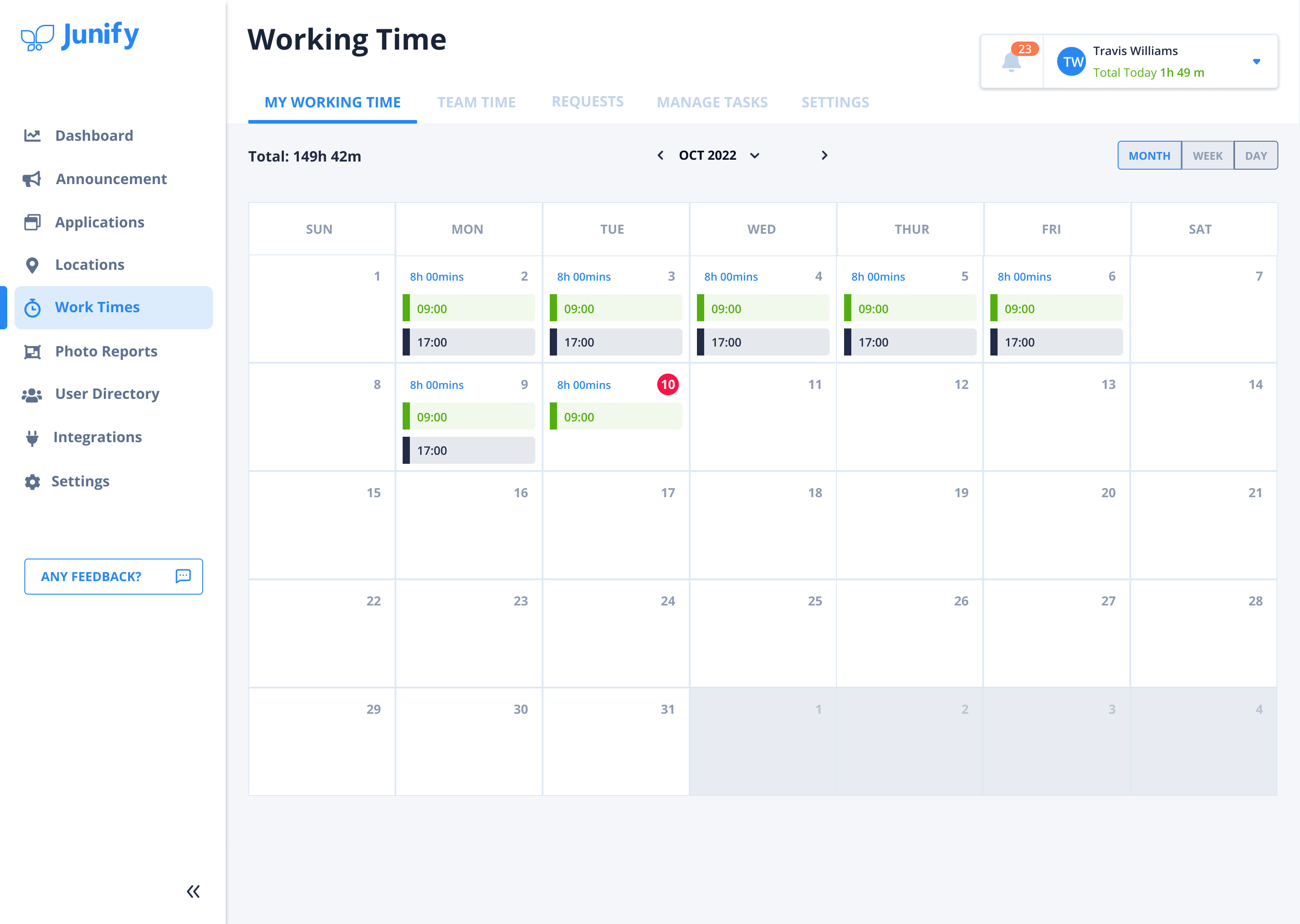
Work Time Management
Provide your staff with an efficient and easy way to clock in and out of work. Export your data into other operational processes, such as payroll and billing.
Time Control
To limit the account used only within specific periods. The time control can be applied for your short-term employee/interns and worried-free when the contract end.
Location Management
For the various use cases, a certain level of security needs the location log to be involved in granting access to the privileged account while working. If your team also does the fashionable delivery business, we can have the record to show the path and how they move in between assigned geofences.
However, the most important thing is that we only log the location while members are working!
Ready to keep your shared account traceable?
Start a Free TrialQuick setup. No credit card required. 30-day free trial.

